How to protect apps from reverse engineering?
In the world of technology, protecting mobile applications has become a buzz among developers. Numerous applications are flooding the market and play store every day, and so do security exposures and threats to the users. Similarly, reverse engineering is a danger that has serious consequences for businesses from concessions on earnings loss and intellectual possession. App developers can incorporate security features in apps to handle threats and keep data safe from hackers.
Things to know about reverse engineering
The procedure in which the binary file turns into an APK file to obtain the source code and other resources is known as reverse engineering. There are tools available that help to convert DEX files decompiled to JAR files and finally into JAVA source code. Many competitors use these tools to steal features and check apps functional abilities. This technique helps the hackers to bypass the authentication process and access premium features of the application. In gaming apps, hackers use this to cheat on other players to get an advantage.
Debuggers like OllyDbg and SoftIce help to track the program flow through which the business logic of the app can be copied in similar mobile applications. Such applications can have malware and the users that download it have their data compromised and stolen.
How to Handle Reverse Engineering?
Today, almost everyone who possesses a smartphone uses mobile applications. Providing security to apps helps to ensure customers use the app. Therefore, developers must adopt new technics to protect mobile apps. These include-
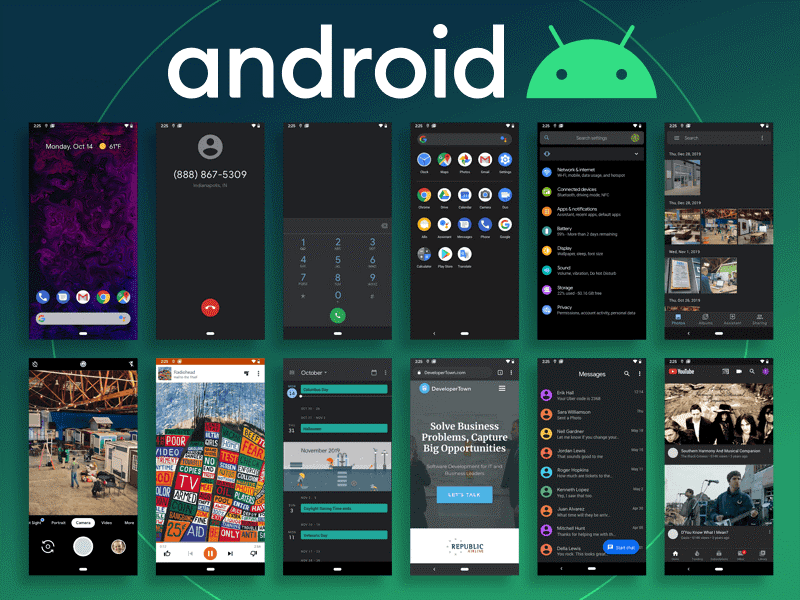
- The programming language developers use to build the app plays a vital role in providing security to applications. C++ or C programming language is used to code functional abilities, which are critical for businesses. The application for androids is usually written in Java programming language, which hackers easily decompile in comparison to C or C++ language. Developers use NDK to write crucial code solely for the files to compile them and start reverse engineering.
- One can also check reverse engineering by using proper techniques to store the code data on the server side. The communication between the server and the app must be through secure APIs.
- Experts recommend using encrypted forms for storing business logic. When you encrypt your code properly, it is only a piece of scrabbling for the hacker who tries to steal your app. This helps to tackle reverse engineering from hackers.
- For storing passwords or important information, it is best to use PBKDF2 or crypt. These powerful hashing algorithms make misuse or decryption impossible.
- Another how to protect app from reverse engineering is to secure the user information in encrypted form. It is crucial to avoid storing such information in the app environment, storage, or in the device. These data are easily accessible to hackers using a USB connection to the device.
- To increase app security, the database must be secured using strong encryption like AES-256 encryption.
- Developers must always hide the API keys and never store them in resource folders. Hardcoded or resource folders can easily be decompiled and zipped for accessing the API key.
Four Key Methods to Ensure App Security
Pro guard helps to secure mobile applications by utilizing licensed servers. Since it is an open-source cross-platform, the hackers find it difficult to reverse the code. Here are four important procedures to ensure complete app security.
Shrink- shrink identifies the unused classes, fields, and methods to remove them.
Optimization- It optimizes and analyses the bytecode by reducing its size and increasing its speed.
Obfuscation- It is used to change names or fields, classes and methods to some meaningless, uncommon, hard to crack names.
Pre Verification- this helps to add the information of pre-verification to classes needed by JAVA 6, JME and more.
How to detect debuggers?
Here are some techniques that developers can use to detect debuggers.
- To check if the identified procedure is debugged-
CheckRemoteDebuggerPresent() Windows API
- NtGlobalFlag Debugger Detection- Here is an easy anti-reversing process to detect debuggers.
- To ensure if the calling procedure is debugged through user-mode debugger-
IsDebuggerPresent() Windows API
- OllyDbg OutputDebugString() Format
- PEB ProcessHeap Flag Debugger Detection
- OllyDbg PE Header Parsing DOS Detection
Obfuscate values once stored on mobile:
Datacollected in mobile applications give a goldmine of information. However,what is an application if it does not have data? This is often wherever obfuscation helps navigate the information protection game smartly. Encryption, tokenization or data masking may well be undertaken to make sure that data is regenerated in a completely different format or structure and kept securely. It focuses on storing data within the type of some algorithmic program or advanced structure. Information storage could be avoided.
Watch out while implementing SSL:
An associate SSL certificate is a digital certificate that helps attest to the identity associated coding of a resource. Understandably, mobile app developers implement SSL certificates for higher code security. May be done by shaping many strategies during a category that implements the SSLSocketFactory interface (in the case of Android). However, since such methods settle for completely different types of certificates, a man-in-the-middle attack is extremely likely. Once Information packets tolerate these certificates, their confidentiality might even be at stake as any skilled hacker can break connections with the assistance of self-signed certificates. Thence caution is suggested while operating with SSLs.
One of the first ways in which to forestall reverse engineering is code obfuscation, which prevents reverse engineering techniques that trust decompiling or dismantling of the app’s code via static or diverse analysis tools like IDA, Hopper and dozens of others. Cryptography obfuscation into your apps is nota straightforward task and needs advanced security skills. For starters, obfuscation may be a unidirectional operation; therefore, if a developer obfuscates the incorrect method or component, the app can break. Secondly, as a result of humans cannot browse code and vice versa, obfuscation usually requires a developer to use symbols to inform machines where to start and finish obfuscation in native supply code. This can be not solely very long to try and do by hand, however should even be properly updated with each new unleash of the app – line by line, release by release.